Building secure and private IoT systems
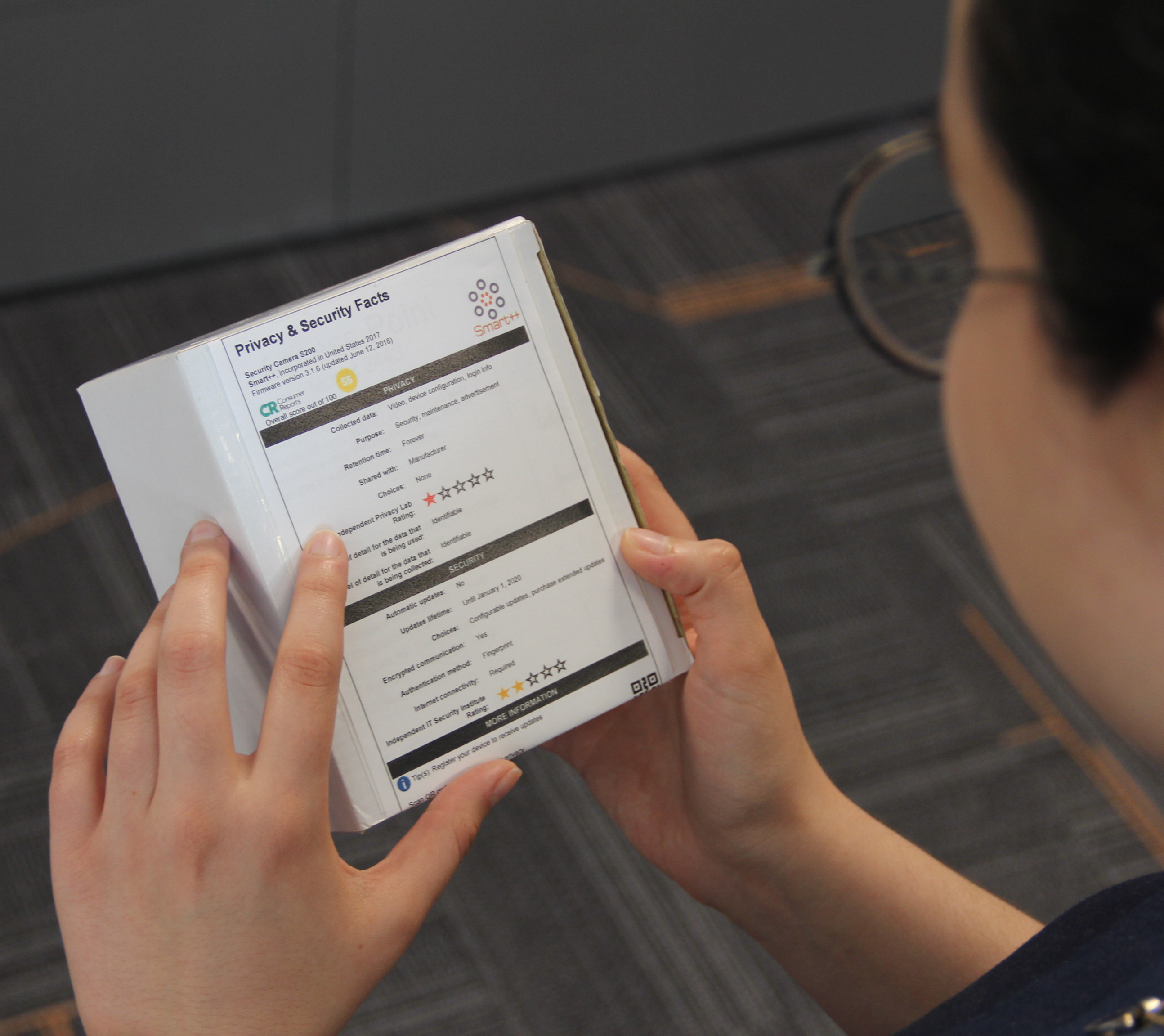
The Internet of Things (IoT) is reaching critical mass in many sectors of the economy, with the prevalence of IoT devices creating significant challenges for the safety, security, reliability, and privacy of consumers and enterprises that use them. Companies currently spend billions on enterprise IoT lifecycle management, but still struggle with security and privacy vulnerabilities, service disruptions, and costly, inefficient, and ineffective remediation methods. Consumers love the convenience of IoT devices, but are increasingly concerned that personally identifiable information is being collected, and that this information may be stolen or misused.
![]()
It is increasingly evident that current approaches are ill-equipped to address the security and privacy challenges that will arise in IoT deployments on several dimensions:
Scalability: Manual security approaches that work for a few hundred IT devices will not scale to billions of IoT devices.
Speed and Cost: Identifying and remediating security vulnerabilities remains largely based upon human effort, thus operates at human-speed of days / months / years – and at human cost. This needs to be automatic, autonomous – taking only seconds or minutes.
Safety and Security: Existing IoT devices may be in service for years, while new greenfield devices are continually being added. New approaches are required to enable ongoing safety and security updates to existing devices without assuming a homogeneous ecosystem.
Uptime and Reliability: IoT devices have specialized functions that require strict uptime (e.g. 24/7 operation) and reliability (low-latency response) guarantees. Unfortunately, they lack management, monitoring and user-interfaces (e.g. keypad and screen) to meet these goals.
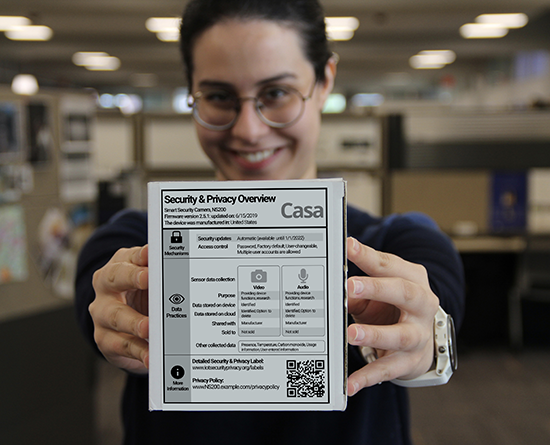
Compliance: IoT devices collect large volumes of raw data, but do not deal with compliance and privacy requirements that arise in deployments. Consumers and enterprises need effective ways to ensure data is collected appropriately, responsibly, and disclosed only as necessary and only to authorized parties.

Explore Other Research Topics