Carnegie Mellon University CyLab researchers are focusing on the security of systems—any systems ranging from the components that make up an autonomous vehicle to the various sectors that make up the energy grid—which requires placing security protocols on different, non-homogeneous parts that must still be able to communicate and work together efficiently and effectively.
People
Learn who at CyLab is working in systems security.
Subtopics
We have researchers working in the following subtopics of applications of security and privacy. Check out each of their research:
- access control and authorization
- automotive and transportation security and privacy
- cloud security
- cyber physical systems security and privacy
- elections security
- embedded systems security
- energy and critical infrastructure security
- intrusion and anomaly detection and prevention
- IoT security and privacy
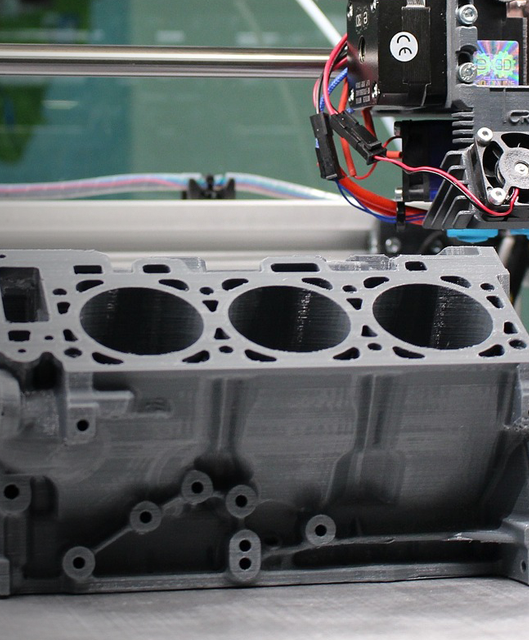
- manufacturing security
- mobile and app security and privacy
- systems security
- web security
Related news
Explore Other Research Topics