CyLab team develops promising tool to help prevent cross-site scripting (XSS) attacks
“These types of attacks are on the rise. We’ve been long-overdue for improving the method by which these vulnerabilities are detected.”
Daniel Tkacik
Feb 21, 2018
Source: CyLab
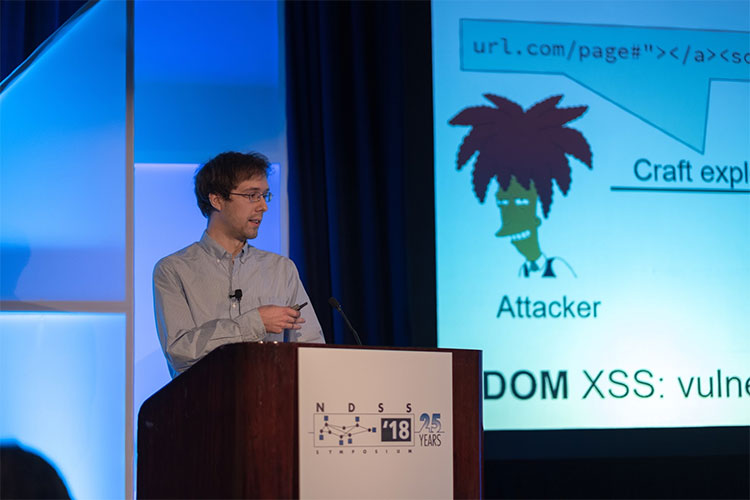
ECE Ph.D. student William Melicher present's the team's study at NDSS in San Diego, CA.
Right now, go to Google.com, search for something (anything) and then look at the search results’ URL. It’s a jumbled mess of numbers, letters, and characters, right? That mess of characters is coordinating the creation of the webpage, displaying a customized list of results based on what you searched for.
On some webpages, attackers have figured out how to insert malicious scripts into the URL. Upon tricking you (an unsuspecting victim) to click on the URL, they can gain access to your personal data. Meet one of the most notorious, common vulnerabilities out there right now: the document object model (DOM)-based cross-site scripting (XSS) attack.
“These types of attacks are on the rise,” says CyLab’s Limin Jia, a professor in Electrical and Computer Engineering (ECE) and the Information Networking Institute (INI). “We’ve been long-overdue for improving the method by which these vulnerabilities are detected.”
In a study presented at this week’s Network and Distributed System Security conference in San Diego, Jia’s team outlines an advanced tool that can help identify parts of webpages that are vulnerable to DOM XSS attacks.
“We found 83 percent more vulnerabilities using our improved methodology versus methodology used in the past,” Jia says.
If you’re a web developer, you can load your page into this modified browser and see if there are problems with your development.
Limin Jia, Professor , Electrical and Computer Engineering (ECE) and the Information Networking Institute (INI)
To understand how Jia’s team did this, it’s important to first understand how a DOM XSS attack is staged. When a webpage contains scripts that execute differently based on the DOM environment (e.g., the page’s URL), and the DOM environment may be changed by an attacker, then attackers can mount a DOM XSS attack by modifying the DOM to include a malicious script. If a user clicks on the attacker-crafted URL, malicious script will then be executed by the user’s browser.
To help identify parts of webpages that are vulnerable to these types of attacks, Jia’s team developed a modified Chromium, a research version of the Google Chrome web browser. It documents potentially dangerous flows from untrusted user input to potentially dangerous places where scripts can execute (e.g., eval), then verifies whether that dangerous flow path can be exploited or not.
“If you’re a web developer, you can load your page into this modified browser and see if there are problems with your development,” Jia says. “Then the developer can re-write the code to avoid the problem.”
Currently, most tools aimed at finding these kinds of vulnerabilities are “static” – that is, they analyze copies of the webpage without rendering the pages in a web browser. According to Jia, static tools are good at finding the easy, “shallow” bugs, but struggle with finding the deeper bugs that can be spotted by their new tool.
Jia’s team is in the process of open-sourcing the tool for developers to use. The source code for the tool will soon be available on GitHub.
