Researchers create new password meter
New password strength meter outperforms state-of-the-art meters and fits in a webpage
Daniel Tkacik
Sep 8, 2016
Is password1! a good password? Many browser-based password meters would say it is, but they’d be wrong.
“It’s just one of many passwords that your typical password meter would classify as strong, when in fact it’s very weak,” says CyLab faculty Lujo Bauer, a professor in the Department of Electrical and Computer Engineering and the Institute for Software Research at Carnegie Mellon University. “Most of the current meters are not based around any principled way of calculating password strength. Doing so usually takes lots of space or lots of time, or both.”
That’s all about to change.
Bauer and a team of researchers in CyLab just published new work outlining a new advanced password meter that makes use of an artificial neural network. The researchers’ study received Best Paper Award at the USENIX Security Symposium.
Source: CyLab
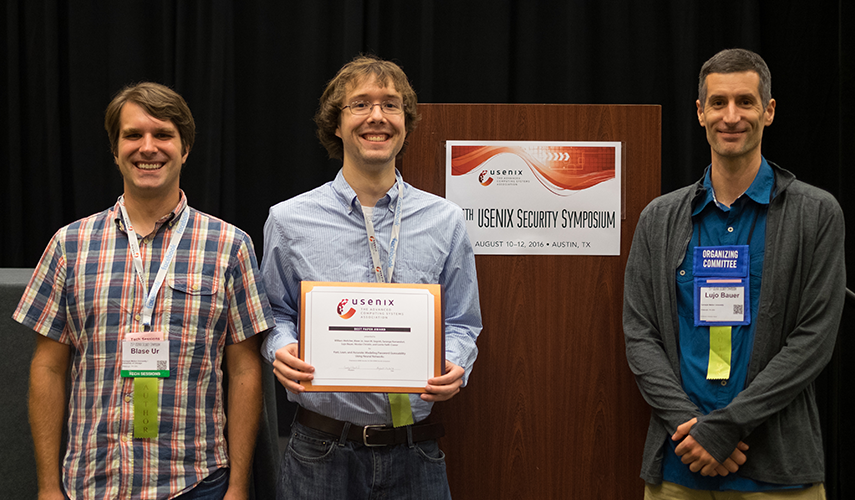
Blaise Ur, Billy Melicher, and Lujo Bauer accepted the Best Paper Aware on their password meter study at the USENIX Security Symposium.
Artificial neural networks map large sets of information in ways that resemble the way neurons behave in the brain. The network “learns” by scanning millions of existing passwords and identifies trends.
“The network might learn that vowels come after consonants, or that if a password contains an exclamation point, it usually happens at the end of a password,” says William Melicher, a Ph.D. student in Electrical and Computer Engineering and lead author of the study.
The researchers showed that their new password model often out-performed some of the best, state-of-the-art password models. What’s more, their model takes up substantially less space than the state-of-the-art models and works in less than a second.
“Previous methods for modeling passwords did not lend themselves to being small enough, but neural networks do,” says CyLab faculty Nicolas Christin, a professor in the Institute for Software Research and the Department of Engineering and Public Policy. “The nice thing about this method of modeling password strength is that it compresses well.”
You also have to give feedback on what people should do to make it stronger when it’s not strong enough.
William Melicher, Ph.D. student, Electrical and Computer Engineering, Carnegie Mellon University
The team compressed their model down to a few hundred kilobytes without substantially worsening guessing effectiveness. Using JavaScript, the team then created the first client-side model of password guessing that is small enough to fit into a webpage. The team open-sourced their model on GitHub.
Moving forward, the team plans on studying the most effective ways of providing users feedback when they are creating passwords.
“One of the interesting things about building a password meter is that having a good measurement of strength is just part of the solution,” says Melicher. “You also have to give feedback on what people should do to make it stronger when it’s not strong enough.”
Other authors on the study included societal computing Ph.D. student Blase Ur, electrical and computer engineering alum Sean Segreti, data scientist and software engineer Saranga Komanduri, and Computer Science and Engineering and Public Policy professor Lorrie Cranor.
